- Home
- Inspiration
Inspiration
- 365DisInFx
- Albeo
- AllSites
- Architectural
- Arize
- Automotive
- Banking
- Building Automation Systems
- Building Control Systems
- Code Compliance
- Commercial Office
- Connected Lighting
- Controls & IoT
- Controls & Sensors
- Current
- Cybersecurity
- Daintree EZ Connect
- Daintree Networked
- Daintree One
- Daintree Wireless Controls System
- Disinfection
- Display & Phosphors
- Distributors
- Downlights
- Education
- Energy Management
- Evolve
- Greenhouse
- Grocery
- Hazardous
- Healthcare
- HID Replacement Lamps
- High Bay
- Horticulture
- Hospitality
- Immersion
- Indoor Farming
- Industrial
- Infrastructure Funding
- Intelligent Environment
- IoT
- LED
- LED Fixtures
- LED Lamps
- LED Tube Replacement
- LED Tubes
- LightGrid
- Lighting Design
- LightSweep
- Low Bay
- Lumination
- News
- Outdoor
- Parking Lot
- Partnerships
- QuickShip
- Recessed
- RefitAdvantage
- Refrigerated Display Lighting
- Retail
- Retrofit
- Roadway
- ROI
- Signage
- Street & Roadway
- Sustainability
- Tetra
- TriGain
- Vertical Farming
- Warehouse
- Webinar
Pagination
-
Current has chosen Illumination Technology Group to represent its GLI Brands, Fixtures in Chicagoland area
Greenville, S.C., April 1, 2024 - Current has chosen Illumination Technology Group as its representative of the GLI Brands,…
-
Current has chosen LightWorks Inc to represent its Roadway Non-Metered Municipal product lines in Southeast Florida.
Greenville, S.C., March 19, 2024 - Current has chosen LightWorks Inc. as its representative for Southeast Florida for…
-
Greenville, S.C., February 15, 2024 - Current has chosen the AM Pacific Agency as its representative for the Province of British Columbia & Yukon Territory for the HLI and GLI luminaire and controls brand portfolios effective…
-
Greenville, S.C., January 31, 2024 - Current has chosen REPCO II as its representative in the Western Pennsylvania and West Virginia commercial lighting markets for HLI Luminaire & Controls Brands. Effective April 1, 2024, this partnership…
-
Greenville, S.C. January 31, 2024 - Current has chosen FRM Lighting + Controls as its representative for South Carolina for the HLI and GLI luminaire and controls brand portfolios effective March 1, 2024.
In addition, FRM Lighting +…
-
When the City of Dover, Ohio converted their aging HID lighting infrastructure to new LED lighting on six of their community baseball fields, the improvement was striking.
The City’s Electric and Parks departments decided to replace the…
-
Greenville, S.C., August 31, 2023 - Current™ has chosen Bell & McCoy Lighting and Controls as its representative in the Texas, Oklahoma, Arkansas, Louisiana, Mississippi, Western Tennessee, and Alabama-Florida-Mississippi Panhandle markets…
-
Baseball is a challenging sport to play. Even the best hitters fail to reach base safely more than half the time. It can be even tougher at night on a poorly lit field, when an outfielder can have trouble seeing the ball as it moves through…
-
Greenville, S.C., Aug. 10, 2023 - Current selects Contact Delage to represent its HLI, GLI and Roadway brand portfolios as the agent for the Province of Quebec. Contact Delage will help Current drive specification of its advanced lighting and…
-
GREENVILLE, S.C., June 1, 2023 — Current announced today that Steve Harris has been appointed as the new CEO of the company, effective May 30, 2023. An experienced business leader and strong operational CEO, Harris succeeds the interim CEO Bill…
-
CLEVELAND – Current today announced three new appointments to the Tetra signage sales team, in order to better serve channel partners, sign fabricators, design firms and brand owners across North America.
Brian Davis has been selected as…
-
CLEVELAND — Current has selected Davis Marketing Associates to be their new agency partner to assist in extending Current’s extensive portfolio of Tetra LED signage lighting products to more sign fabricators throughout the Northeastern, Mid-…
-
SAN FRANCISCO October 27, 2022 – Current Chemicals is unveiling market-ready miniLED LCD displays with phosphor film at the Phosphors & Quantum Dots Industry Forum 2022 in San Francisco this week. These displays are high contrast and wide…
-
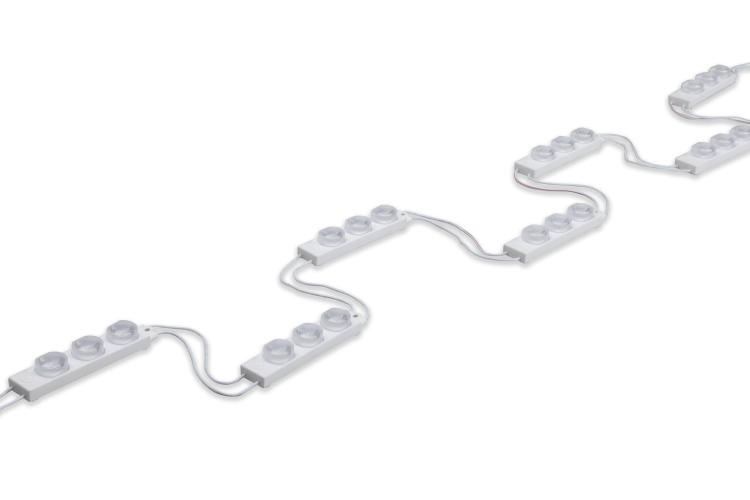
Current Lighting is ready to unveil its new products: Tetra® Slim EdgeStrip and Tetra® EdgeLine.
Tetra® Slim EdgeStrip is an LED system that is designed for single- or double-sided Cabinet Signs, and Tetra® EdgeLine is a slim wall wash fixture…
-
Current Lighting is ready to unveil its new and updated LED border lighting systems: Tetra® Contour Flex and Tetra® Contour Gen 2.
Tetra® Contour Flex is a flexible LED system that can easily be formed to fit a wide variety of designs and…